The moment you buy your first bitcoin or Ethereum, you inherit a responsibility that traditional banking has always handled for you: securing your money. Except now there’s no bank. No customer service line. No FDIC insurance. Just you, a private key, and a brutal truth—in cryptocurrency, if you lose your keys, you lose your money permanently. No recovery. No recourse.
Understanding the difference between hot wallets and cold wallets is foundational knowledge for anyone holding crypto. Get this wrong, and it doesn’t matter how carefully you pick your investments—because someone will take them, or you’ll lock yourself out of your own holdings, and both outcomes are equally permanent.
This guide covers both wallet types, what they’re good at, where they fail, and how to combine them into a security strategy that fits your situation. I’m not trying to sell you on the “best” wallet—I’m trying to help you understand trade-offs that most articles on this topic either oversimplify or bury under marketing fluff.
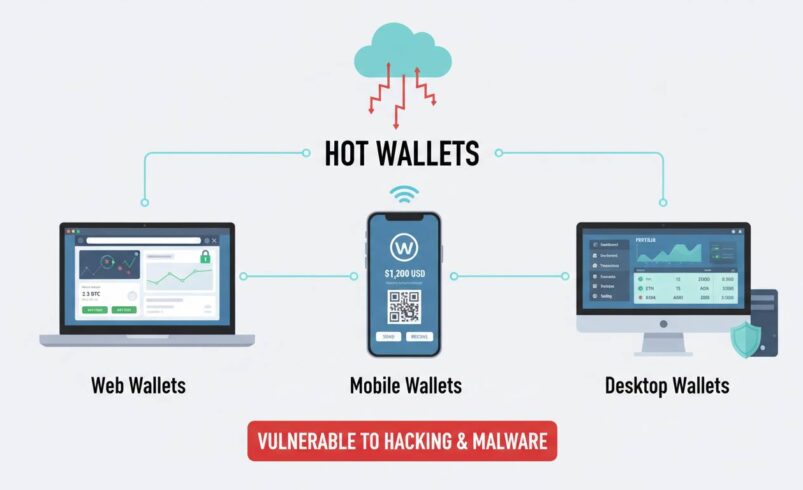
What Is a Hot Wallet?
A hot wallet is any cryptocurrency wallet that remains connected to the internet. That’s the simplest definition, and it’s the only one that matters for understanding the security implications. Your private keys—the cryptographic credentials that prove you own your crypto—sit on a device or service that can theoretically be reached by anyone with the right exploit, phishing attack, or malware.
Hot wallets come in several forms. Exchange wallets are the most common entry point because every major cryptocurrency exchange (Coinbase, Binance, Kraken) provides one automatically when you create an account. These are convenient because you can buy, sell, and trade instantly without moving funds anywhere. The tradeoff is that you don’t actually control your private keys—the exchange does. When you hold crypto on an exchange, you’re essentially an unsecured creditor to that platform. If they get hacked, go bankrupt, or freeze your account for any reason, your options are limited and often expensive.
Software wallets represent the next tier. MetaMask, Exodus, and Trust Wallet are popular examples. These install as browser extensions or mobile apps on your personal device. You control your keys, which means you’re the only one who can authorize transactions. But your device becomes a target—malware, keyloggers, clipboard hijackers, and malicious apps all represent attack vectors that didn’t exist when you were just checking your bank account.
The practical reality is that hot wallets excel at one thing: frequent transactions. If you’re day trading, moving funds between DeFi protocols, or regularly buying and selling, the convenience of instant connectivity is genuinely valuable. But treating a hot wallet as your primary storage for anything beyond small amounts you’re actively trading with is a security decision that will eventually cost you.
What Is a Cold Wallet?
A cold wallet keeps your private keys completely disconnected from the internet. That’s the core distinction, and it’s the reason cold wallets are considered the gold standard for cryptocurrency security. No internet connection means no remote hackers, no malware, no phishing attacks that target your wallet software directly. The private keys exist in isolation, typically on a specialized hardware device or even on paper.
Hardware wallets are the most practical cold storage option for most users. Companies like Ledger and Trezor manufacture small devices that generate and store your private keys in a secure element—a tamper-resistant chip that never exposes your keys to the computer or phone they’re connected to. When you want to sign a transaction, the hardware wallet handles the cryptographic operation internally and only transmits the signed result to your connected device. Your keys never leave the device, and the device never connects to a network directly.
The most security-conscious users go even further. Paper wallets—where you generate a private key and its corresponding address, then print them on paper and destroy all digital copies—represent true cold storage at its most paranoid. Air-gapped computers (machines that have never and will never connect to the internet) can also generate and store keys. Some people engrave their private keys into metal plates that can survive fires and floods. These approaches all share a common philosophy: if something can’t be reached electronically, it can’t be stolen electronically.
Cold wallets have one obvious drawback: accessibility. Moving funds out of cold storage requires physical access to your hardware device, manual confirmation of transactions, and usually a process that takes several minutes rather than seconds. For someone managing a portfolio across multiple wallets, interacting with DeFi protocols daily, or taking advantage of market opportunities that require fast execution, this friction can be genuinely problematic.
Security Comparison: What You’re Actually Risking
Let’s be direct about the threat landscape, because vague warnings about “hackers” don’t help you make informed decisions.
Hot wallet vulnerabilities fall into several categories. Exchange hacks have historically been the biggest source of losses—Mt. Gox in 2014 lost 850,000 bitcoin (worth roughly $450 million at the time), and the pattern has repeated dozens of times since. Even major exchanges like Coincheck ($534 million in 2018) and FTX (the collapse in 2022 wasn’t a hack, but users lost access to billions in funds) have demonstrated that trusting a third party with your keys is a fundamentally different risk than self-custody. Beyond exchange failures, your personal hot wallet faces malware targeting clipboard data (replacing a copied wallet address with the attacker’s address), browser extensions that inject malicious transaction data, mobile apps that exfiltrate keys, and SIM-swapping attacks that hijack your phone number to bypass two-factor authentication.
Cold wallet threats are fundamentally different because they require physical access. Someone needs to obtain your hardware device and either steal it while you use it (to compromise the PIN) or tamper with it before you receive it. Ledger’s 2020 data breach (exposing 272,000 customer names, addresses, and phone numbers) led to sophisticated social engineering attacks where scammers called victims pretending to be Ledger support and convinced them to reveal their recovery phrases. The attack wasn’t a flaw in Ledger’s security architecture—it was a breach of their customer database exploited through human psychology. This matters because it reveals an uncomfortable truth: cold wallets protect you from remote digital attacks, but they can’t protect you from phishing, social engineering, or your own mistakes in handling recovery phrases.
The comparison table below summarizes the key differences:
| Factor | Hot Wallet | Cold Wallet |
|---|---|---|
| Internet Connectivity | Always connected | Offline by design |
| Primary Threat | Remote hacking, malware, exchange failure | Physical theft, social engineering |
| Convenience | High | Low |
| Transaction Speed | Instant | Minutes |
| Best For | Trading, small amounts, DeFi interactions | Long-term storage, large holdings |
| Recovery | Usually tied to account/seed | Recovery phrase only |
| Cost | Usually free | $50-$250+ |
The Recovery Phrase Problem Nobody Talks About
Most articles about cold wallets treat the recovery phrase (also called a seed phrase or mnemonic phrase) as a simple backup—write down 24 words, store them somewhere safe, done. This is dangerously incomplete advice.
Your recovery phrase is the master key to everything. If you have your crypto in a hardware wallet and someone obtains your 24-word recovery phrase, they have your crypto. The hardware device becomes irrelevant. Your PIN becomes irrelevant. The hardware wallet was never actually protecting your keys—it was protecting the derivation path from your recovery phrase to your actual private keys. Hand over the phrase, and you hand over everything.
This creates a security paradox that’s nearly impossible to solve perfectly. You need to store your recovery phrase somewhere accessible enough that you or your heirs can find it, but secure enough that no one else can. A safe deposit box? Accessible by bank employees with court orders. A home safe? Vulnerable to burglars. A hidden location in your home? You’ll forget where you put it, or die unexpectedly and leave your family with no way to access your estate. Fireproof safes can fail. Soil can degrade paper. Digital backups get corrupted or hacked.
Some solutions have emerged. Cryptosteel and similar products let you assemble your recovery phrase from individual metal letter tiles, surviving fires up to around 1,400°C. Multi-signature setups require multiple keys to authorize transactions—a 2-of-3 scheme, for instance, means any two of three designated signers must approve a transfer. Services like Casa offer managed multi-signature solutions specifically designed for inheritance planning. But none of these are foolproof, and the complexity of setting them up correctly creates its own risks—you can lock yourself out just as easily as an attacker can steal your funds.
The honest truth is that every crypto holder needs to accept that their recovery phrase is the weakest link in their security setup. The wallet itself is secure. The network is secure. The cryptography is secure. But humans are not secure, and our storage solutions for these ultra-sensitive pieces of information are constantly tested by both technical and social attacks.
When Hot Wallets Make Sense (And When They Don’t)
I’ve been deliberately negative about hot wallets because the marketing around them vastly understates the risks. But that doesn’t mean they’re useless—it means they’re useful in specific contexts that most people get wrong.
A hot wallet makes sense for what I call “working capital” amounts. This is the cryptocurrency you’re actively trading, the amount you’re using to explore DeFi protocols, or the funds you need to access quickly for arbitrage or opportunity capture. There’s no precise number that works for everyone—it depends on your total portfolio, your risk tolerance, and your emotional capacity to absorb losses. A reasonable heuristic: if losing this amount would meaningfully impact your life, it’s too much for a hot wallet.
Exchange wallets are particularly problematic even for working capital because they add counterparty risk on top of technical risk. If you’re actively trading, using a software wallet like MetaMask or Rabby gives you custody of your own keys while maintaining the convenience of instant transactions. Exchange wallets should be treated as temporary holding areas—deposit funds, execute trades, withdraw to your own wallet. The longer your funds sit on an exchange, the more exposure you have to their operational risks.
What doesn’t make sense is storing your life savings in a hot wallet because “it’s easier” or because you’re afraid of the complexity of cold storage. The 15 minutes it takes to set up a hardware wallet could save you from catastrophic loss. If you’re holding more than you can afford to lose—and this threshold is different for everyone—you have an ethical obligation to yourself to use appropriate security.
When Cold Wallets Make Sense (And Their Real Limitations)
Cold wallets are the right choice for any cryptocurrency you’re holding as a long-term investment. If you’ve bought bitcoin or Ethereum with the intention of holding it for years, cold storage is the only serious option. The friction of accessing it becomes irrelevant because you’re not accessing it frequently.
But here’s where I see people make expensive mistakes. They buy a hardware wallet, set it up, transfer their life savings to it, and then… stop. They never test the recovery process. They don’t verify that their backup works. They don’t practice the transaction flow. Then when they need to use it—maybe years later—there’s a problem. Maybe their computer’s USB ports don’t work properly. Maybe the Ledger or Trezor software has updated and they don’t remember their PIN. Maybe the device fails and they discover their written-down recovery phrase was incomplete or illegible.
Test your setup while it’s still easy to fix. Transfer a small amount, practice the full transaction flow from cold storage to a known working address, then restore your wallet from the recovery phrase on a fresh device or different computer. This isn’t paranoia—it’s operational security. The time to discover a problem is not during an emergency when markets are moving and you need to act fast.
Another limitation worth acknowledging: cold wallets don’t protect you from yourself in the way you might expect. If someone physically threatens you and demands you unlock your hardware wallet, a cold wallet provides no defense. The PIN delay feature (which locks the device after multiple failed attempts) is a minor obstacle at best. True threat models need to consider physical security, personal safety, and the possibility that coercion exists beyond what any wallet can defend against.
Building a Layered Security Strategy
The concept is simple: don’t put all your crypto in one basket. The execution requires actual thought about what you’re protecting against and what level of access you need.
A practical three-tier approach looks like this. First, keep a small amount in your hot wallet for daily transactions—this might be $100 or $1,000 depending on your activity level. Accept that this money could disappear and plan accordingly. Second, maintain a moderate amount in a software wallet that you control with your own keys—this is your working capital for trading and DeFi activities. Third, move the bulk of your holdings to cold storage on a hardware wallet. Some users extend this further, using separate hardware wallets for different assets or maintaining geographically distributed backups of their recovery phrases.
Multi-signature setups add another layer for significant holdings. Services like Unchained Capital or Casa let you set up wallets that require multiple approvals for any transaction. A 2-of-3 setup means you need two of three designated keys to move funds. You could keep one key on a hardware wallet at home, one at a trusted family member’s location, and one with a professional custodian. This protects against both theft and loss—if your house burns down, you can still recover your funds using the other two keys.
Hardware Wallet Recommendations: What Actually Works
I’m intentionally avoiding detailed product recommendations in most of this article because the right choice depends on your specific situation and the landscape changes frequently. But I can tell you what matters when evaluating hardware wallets and point you toward the major players that have proven track records.
Ledger devices (the Nano S Plus and the Nano X) have the largest market share and the most extensive third-party integration. Their proprietary Secure Element chip has undergone extensive testing, though the 2020 breach I mentioned earlier exposed the uncomfortable reality that even security-focused companies can have their customer data compromised. Trezor devices (the Model One and Model T) offer open-source firmware, meaning anyone can inspect the code for vulnerabilities—a philosophical advantage for users who prioritize transparency over convenience.
What doesn’t work: buying used hardware wallets, purchasing from unauthorized resellers, or accepting a device that arrives in packaging that looks tampered with. The supply chain matters. Only buy directly from the manufacturer. Only buy new. When you first receive it, verify the packaging hasn’t been compromised before you even plug it in.
The honest assessment is that both Ledger and Trezor have strong security track records relative to the industry. The more important variable is your own operational security—how carefully you handle your recovery phrase, how you test your setup, and whether you’re alert to social engineering attempts that target human psychology rather than technical vulnerabilities.
Common Mistakes That Cost People Money
The cryptocurrency security literature is full of warnings that sound obvious in retrospect but get ignored in practice. Let me highlight the ones I see most frequently destroy portfolios.
Writing your recovery phrase on a sticky note that then gets photographed, thrown away, or accidentally seen by someone who later becomes an adversary. Digital photos of recovery phrases are searchable—malware specifically scans image galleries for patterns matching seed phrases. Never store your recovery phrase digitally. Never.
Failing to update wallet software. Both Ledger and Trezor regularly release firmware updates that patch newly discovered vulnerabilities. Running outdated firmware is like leaving your front door unlocked because the lock was secure when you installed it five years ago.
Clicking links in direct messages, emails, or Discord servers that ask you to connect your wallet or enter your seed phrase. This is so obvious and so commonly repeated that people stop taking it seriously—and that’s exactly when they get caught.
Sending transactions to the wrong address. Cryptocurrency transactions are irreversible. If you type an address incorrectly or paste a corrupted address from your clipboard, your funds are gone. Always verify the first few and last few characters of any address before confirming.
Ignoring the human element. Security technology is only as good as the person using it. If you’re storing your recovery phrase in a way that a sophisticated attacker couldn’t find, but your spouse doesn’t know where it is and you’re in an accident, your crypto becomes effectively inaccessible. Balance security against usability, and make sure trusted people know enough to help you if you become incapacitated.
Frequently Asked Questions
Can hot wallets be hacked?
Yes. Hot wallets are internet-connected, which means they’re vulnerable to remote attacks. Exchange hot wallets have been hacked for billions of dollars collectively. Software wallets on personal devices are vulnerable to malware, phishing, and various forms of key theft. Using a hot wallet means accepting that risk as a tradeoff for convenience.
Is it safe to keep crypto on an exchange?
No. Exchanges are high-value targets and have a history of both hacks and operational failures. Holding cryptocurrency on an exchange means you’re trusting a third party with your funds—an arrangement that has repeatedly failed. If you must use an exchange for trading, withdraw to your own wallet when you’re not actively trading.
Do cold wallets need to be updated?
Hardware wallets require periodic firmware updates to patch security vulnerabilities. These updates are delivered through the manufacturer’s software when the device is connected to a computer. Always verify you’re downloading the legitimate update tool from the official source—attacks have been attempted through fake update websites.
What happens if I lose my hardware wallet?
Your funds are safe as long as you have your recovery phrase. You can purchase a new hardware wallet (or use compatible software) and restore your funds using the 24-word phrase. This is why the recovery phrase backup is critical—without it, a lost or damaged device means permanent loss.
Can cold wallets be hacked while offline?
Theoretically, but it’s extraordinarily difficult and requires physical access to the device. A sophisticated attacker with the device in hand could potentially exploit hardware vulnerabilities to extract keys, but this is far beyond the capability of typical thieves or hackers. The more likely attack vector on cold wallets is social engineering to obtain your recovery phrase, not technical hacking of the device itself.
Should I tell my family about my crypto holdings?
This is a personal decision, but it’s one of the most practical security measures you can take. If something happens to you and no one knows you own cryptocurrency or where to find your recovery phrase, those assets become effectively lost. At minimum, a trusted family member should know you hold crypto and where to find basic documentation—without necessarily knowing the specific amounts or exact recovery phrase location.
Looking Forward: What’s Actually Changing
The wallet security landscape continues to evolve, and several developments are worth watching as of early 2025.
Multi-signature and social recovery solutions are becoming more accessible. Services that let you designate trusted contacts who can help recover your funds—without giving any single person full control—are moving from early-stage experiments to genuinely usable products. This addresses the recovery phrase problem: rather than trusting one piece of paper with everything, you can distribute trust across multiple people or devices.
Custodial solutions are also maturing, with some regulated platforms now offering insurance and regulated custody options that appeal to institutional investors and wealthy individuals who want professional security without managing their own keys. These come with their own trade-offs (counterparty risk, limited control), but they represent an option that didn’t exist meaningfully a few years ago.
The intersection of decentralized finance and self-custody remains a tension point. Using cold wallets means missing out on yield opportunities, staking rewards, and DeFi participation that require connected funds. Some hardware wallet manufacturers are addressing this by building devices that can interact with DeFi protocols while keeping keys secure, but the user experience still has meaningful friction compared to hot wallet alternatives.
The honest reality is that there’s no perfect solution—only trade-offs that you need to understand and choose between based on your specific situation, your technical comfort level, and what you’re actually trying to protect against.
Your cryptocurrency security setup should evolve as your holdings grow and as the threat landscape changes. What feels like overkill when you’re learning with $100 becomes essential when that $100 becomes $10,000. Start with the basics: understand the difference between hot and cold storage, use a hardware wallet for anything you plan to hold for more than a few days, and—most importantly—practice your security procedures while the stakes are low enough that mistakes are recoverable. The time to figure out how your wallet works is not during an emergency.
The reality is that cryptocurrency gives you unprecedented control over your own finances—and that control comes with responsibility that most people enter this space completely unprepared for. That’s not a reason to stay out. It’s a reason to take the learning seriously from day one.